FIELD MANUAL
SQL: The Language of Data
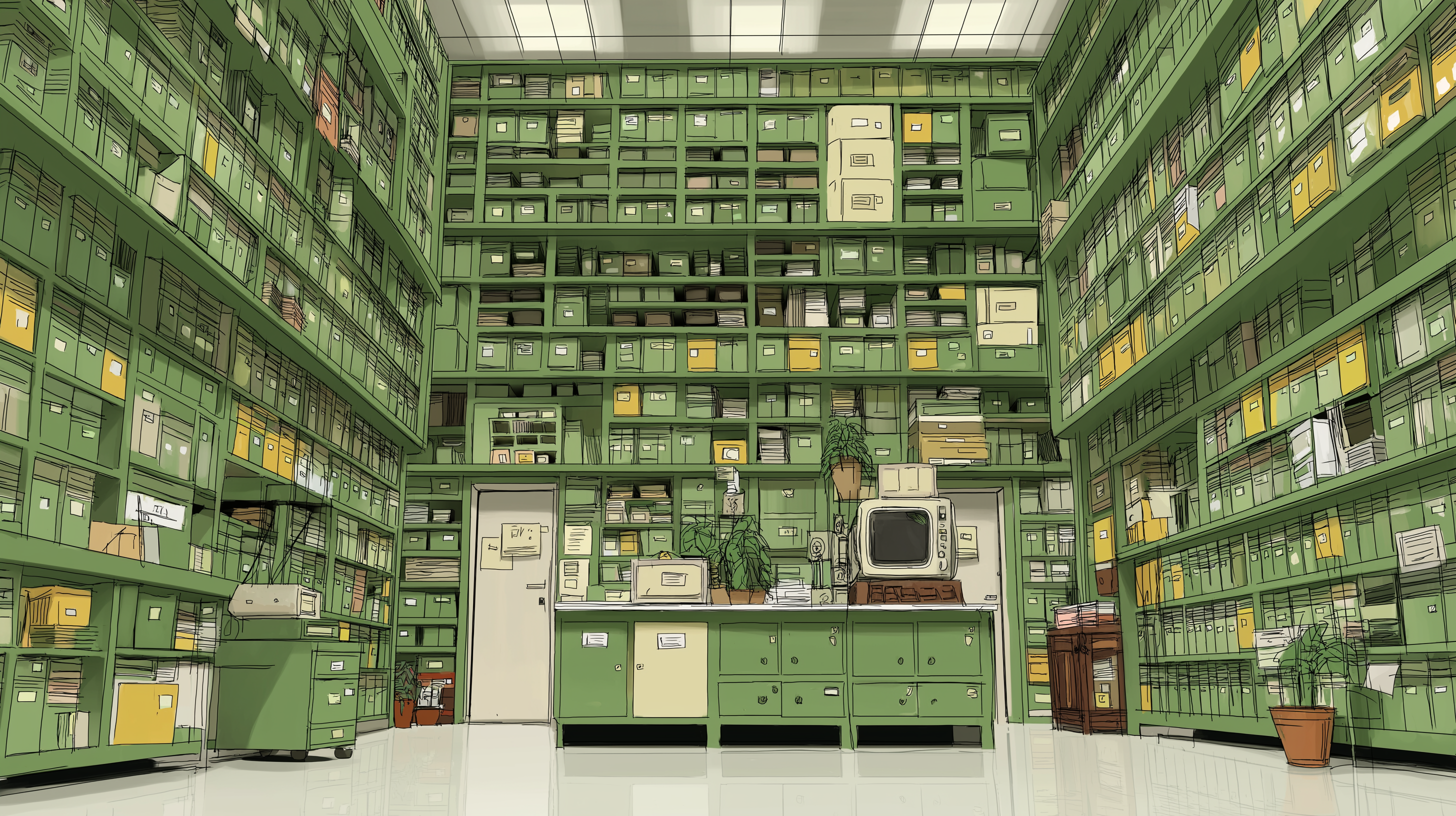
Databases: The Vaults of the Internet
Databases · 6 chapters · Queries → SQL Injection
Incoming transmission
Every web application you use runs on a database. Instagram, your bank, your email — all of it is SQL underneath. The attacker who hit Coastal Data Systems didn't crack any encryption or run sophisticated exploits. They typed a few characters into a search box, and the database handed over everything.
Six chapters. We start with what a database actually is and work up to how attackers exploit the one mistake developers keep making. By the end, you'll be able to read a SQL query, understand what it's doing, and spot an injection vulnerability when you see one.
— Commander Shepard